WireSock Secure Connect — Advanced Configuration Parameters
NOTE
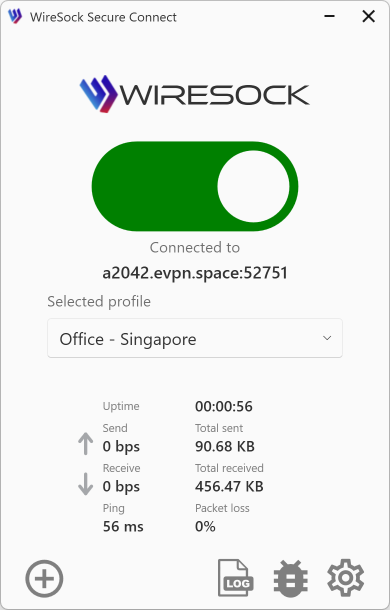
This documentation describes the advanced parameters for VPN Client – WireSock Secure Connect, intended for situations where you prefer to edit configuration files manually.
All of the parameters shown here can also be set through the GUI version of WireSock Secure Connect, which you can download from our official site. See the step-by-step GUI instructions here.
WireSock Secure Connect lets you fine-tune your tunnel by enabling you to:
- Define the traffic scope that should be routed through the VPN.
- Specify applications permitted to use (or excluded from) the tunnel.
- Exclude IP addresses or ranges from the VPN.
- Route the WireGuard handshake via a SOCKS 5 proxy for extra obfuscation.
WireSock-specific directives live in the same WireGuard .conf file that holds your standard [Interface] and [Peer] blocks. A full overview of generic WireGuard syntax is available here.
Compatibility Prefix
To ensure the configuration remains compatible with third-party WireGuard clients that do not recognize WireSock-specific directives, you can prefix any WireSock-only line with #@ws:. The WireSock client will parse these lines, while other clients treat them as harmless comments.
# Standard WireGuard options ...
[Peer]
PublicKey = SERVER_PUBLIC_KEY
Endpoint = vpn.example.com:51820
AllowedIPs = 0.0.0.0/0, ::/0
# [Peer] WireSock extensions
#@ws:DisallowedApps = Discord
#@ws:Socks5Proxy = proxy.example.com:1080WireSock-Specific Parameters
(The following sections include only parameters unique to WireSock Secure Connect)
AllowedApps (Optional)
Section [Peer]
Define the applications that are authorized to use the VPN tunnel.
GUI equivalent: this setting corresponds to the “Tunneled applications” section in the WireSock Secure Connect interface.
Specify your applications by listing them separated by commas. It’s not necessary to include the .exe extension for process names. If your entry includes slashes (/) or backslashes (\), the system will recognize it as a full pathname. Providing a full pathname allows you to target a specific folder, automatically including all executables within that directory for convenience.
NOTE
If not set, the VPN tunnel is available to all applications.
Examples:
- Full path:
C:\Program Files (x86)\Google\Chrome\Application\chrome.exe - Process names:
chrome, msoffice, firefox - All applications in Program Files folder:
C:\Program Files
Dependency: Must be paired with AllowedIPs to define the scope of traffic for these applications.
Example of configuration:
[Interface]
PrivateKey = [Your Private Key Here]
Address = 10.66.66.2/32, fd42:42:42::2/128
DNS = 94.140.14.14, 94.140.15.15
MTU = 1420
[Peer]
PublicKey = [Peer Public Key Here]
AllowedIPs = 0.0.0.0/0, ::/0
Endpoint = [VPN Endpoint Here]:51820
# [Peer] WireSock extensions
#@ws:AllowedApps = chrome, msoffice
#@ws:DisallowedIPs = 192.168.1.0/24DisallowedApps (Optional)
Section [Peer]
List the applications that are barred from using the VPN tunnel.
GUI equivalent: this setting corresponds to the “Non-tunneled applications” section in the WireSock Secure Connect interface.
Provide your applications by listing them separated by commas. Including the .exe extension for process names is not necessary. If an entry contains slashes (/) or backslashes (\), the system will interpret it as a full pathname. Specifying a full pathname allows you to target a specific folder, automatically excluding all executables within that directory for convenience.
NOTE
If both AllowedApps and DisallowedApps are specified, AllowedApps is prioritized and evaluated first.
Examples:
- Full path:
C:\Program Files (x86)\Google\Chrome\Application\chrome.exe - Process names:
chrome, msoffice, firefox - All applications in Program Files folder:
C:\Program Files
Example of configuration:
[Interface]
PrivateKey = [Your Private Key Here]
Address = 10.66.66.2/32, fd42:42:42::2/128
DNS = 94.140.14.14, 94.140.15.15
MTU = 1420
[Peer]
PublicKey = [Peer Public Key Here]
AllowedIPs = 0.0.0.0/0, ::/0
Endpoint = [VPN Endpoint Here]:51820
# [Peer] WireSock extensions
#@ws:AllowedApps = C:\Program Files
#@ws:DisallowedApps = msoffice
#@ws:DisallowedIPs = 192.168.1.0/24DisallowedIPs (Optional)
Section [Peer]
Identify IP addresses and ranges that should not use the VPN tunnel.
GUI equivalent: this setting corresponds to the “Non-tunneled networks/addresses” section in the WireSock Secure Connect interface.
This parameter excludes specified IP addresses and ranges from the tunnel.
List the IPs and ranges separated by commas, such as 1.1.1.1, 192.168.1.0/24.
For example, if you want to access your local network, you can exclude it from the tunnel by adding 192.168.1.0/24 to the DisallowedIPs parameter.
NOTE
If AllowedApps is configured, DisallowedIPs will prevent the listed IPs and ranges from being tunneled for those applications.
Example of configuration:
[Interface]
PrivateKey = [Your Private Key Here]
Address = 10.66.66.2/32, fd42:42:42::2/128
DNS = 94.140.14.14, 94.140.15.15
MTU = 1420
[Peer]
PublicKey = [Peer Public Key Here]
AllowedIPs = 0.0.0.0/0, ::/0
Endpoint = [VPN Endpoint Here]:51820
# [Peer] WireSock extensions
#@ws:AllowedApps = C:\Program Files
#@ws:DisallowedIPs = 192.168.1.0/24, 1.1.1.1SOCKS5 Proxy
Section [Peer]
For users needing to route their WireGuard handshake through a SOCKS5 proxy, additional parameters are provided:
- Socks5Proxy: Set the SOCKS5 proxy endpoint, e.g.,
socks5.sshvpn.me:1080or an IP-based endpoint like13.134.12.31:1080. - Socks5ProxyUsername: (Optional) Specify the proxy username.
- Socks5ProxyPassword: (Optional) Specify the proxy password.
- Socks5ProxyAllTraffic: (Optional) When set to
true(e.g.,Socks5ProxyAllTraffic = true), it forces all WireGuard traffic through the SOCKS5 proxy, effectively masking it from DPI detection.
Example of configuration:
[Interface]
PrivateKey = [Your Private Key Here]
Address = 10.66.66.2/32, fd42:42:42::2/128
DNS = 94.140.14.14, 94.140.15.15
MTU = 1420
[Peer]
PublicKey = [Peer Public Key Here]
AllowedIPs = 0.0.0.0/0, ::/0
Endpoint = [VPN Endpoint Here]:51820
# WireSock Socks5 Proxy extension
#@ws:Socks5Proxy = socks5.sshvpn.me:1080
#@ws:Socks5ProxyUsername = myusername
#@ws:Socks5ProxyPassword = mypassword
#@ws:Socks5ProxyAllTraffic = trueJunk packets
Section [Interface]
Junk packets are dummy or random packets sent alongside real VPN traffic. Their purpose is to mask the traffic’s size, timing, and structure, making it more difficult for Deep Packet Inspection (DPI) systems to identify VPN usage. This reduces the risk of VPN traffic being detected or blocked. Junk packets are a DPI protection technique that works with standard WireGuard servers.
The behavior of junk packets is controlled by the following parameters: Jc, Jmin, Jmax, and Jd (where Jc, Jmin, and Jmax follow the AmneziaWG extension). Default values:
Jc= 3Jmin= 50Jmax= 1000Jd= 0
If Jc is set to 0 or is not specified, junk packets are not sent.
Junk packet count (Jc)
- Description: Junk packet count (Jc) specifies the number of junk packets to send before the actual VPN session begins.
- Recommended value: Jc = 3-10.
- If Jc is set to zero then no junk packets are sent, and the protocol operates similarly to standard WireGuard.
Junk packet minimum size (Jmin)
- Description: Junk packet minimum size (Jmin) - defines the minimum byte sizes for each junk packet.
- Jmin is typically set to 50 bytes.
Junk packet maximum size (Jmax)
- Description: Junk packet maximum size (Jmax) - defines the maximum byte sizes for each junk packet.
- Jmax is typically set to 1000 bytes.
Junk packets delay (Jd)
- Description: Junk packets delay (Jd) - delay (in milliseconds) between junk packets sent before the handshake.
- Default value is 0
[Interface]
PrivateKey = [Your Private Key Here]
Address = 10.66.66.2/32, fd42:42:42::2/128
DNS = 94.140.14.14, 94.140.15.15
MTU = 1420
# Amnezia WG extension
Magic Headers (AmneziaWG)
Section [Interface]
Magic Headers are a feature of the AmneziaWG protocol that enhance traffic obfuscation by adding random data to handshake packets and modifying specific WireGuard fields. This makes VPN traffic resemble other network protocols, helping it avoid detection. All parameters (S1, S2, H1, H2, H3, and H4) must be specified for a valid Amnezia configuration.
If both S1 and S2 are set to 0, no headers will be added.
NOTE
Important:
- Magic Headers must be set on both client and server and are incompatible with standard WireGuard servers.
- All parameters S1-S2, H1-H4 must not be empty to configure Magic Headers.
NOTE
For the most up-to-date information about the S1–S4 and H1–H4 parameters, please refer to the official Amnezia documentation
Init packet junk size (S1)
- Description: Init packet junk size (S1) determines the amount of random data appended to the initiation handshake packet, altering its size to evade detection.
- If not specified, S1 defaults to 0, meaning no additional junk data is added.
Response packet junk size (S2)
- Description: Response packet junk size (S2) specifies the amount of random data added to the response handshake packet, modifying its size for obfuscation.
Init packet magic header (H1)
- Description: Init packet magic header (H1) sets a custom header for the initial handshake packet sent from the client to the server.
- Each header (H1, H2, H3, H4) must be unique to prevent predictable sequences.
Response Packet Magic Header (H2)
- Description: IResponse Packet Magic Header (H2) defines a custom header for the handshake response packet sent from the server to the client.
- Each header (H1, H2, H3, H4) must be unique to prevent predictable sequences.
Transport Packet Magic Header (H3)
- Description: Transport Packet Magic Header (H3) specifies a custom header for data packets transmitted during the VPN session.
- Each header (H1, H2, H3, H4) must be unique to prevent predictable sequences.
Underload Packet Magic Header (H4)
- Description: Underload Packet Magic Header (H4) Sets a custom header for underload packets, which are specific control packets used within the AmneziaWG protocol.
- Each header (H1, H2, H3, H4) must be unique to prevent predictable sequences.
[Interface]
PrivateKey = [Your Private Key Here]
Address = 10.66.66.2/32, fd42:42:42::2/128
DNS = 94.140.14.14, 94.140.15.15
MTU = 1420
# Amnezia WG extension
Protocol Masking
Section [Interface]
Protocol Masking is a technique that disguises VPN traffic as regular UDP traffic. In this mode, VPN traffic is made to look like typical browser traffic (for example, from Chrome or Firefox) communicating with a website using common protocols such as QUIC or DNS.
To use Protocol Masking effectively, you need to select a working combination for your region, including the masking domain, the protocol, and the browser profile to be mimicked.
Domain for masking
- Description: The domain name used to mask VPN traffic.
- Recommended value: It should be a popular domain in your region (for example, a major e-commerce platform).
Protocol for masking
- Description: The protocol used to mask VPN traffic.
- Supported protocols: QUIC and DNS.
Browser for masking
- Description: The browser used to mask VPN traffic.
- Valid options: Chrome, Firefox, cURL.
- This option is available only when the QUIC protocol is selected.
[Interface]
PrivateKey = [Your Private Key Here]
Address = 10.66.66.2/32, fd42:42:42::2/128
DNS = 94.140.14.14, 94.140.15.15
MTU = 1420
# Protocol masking